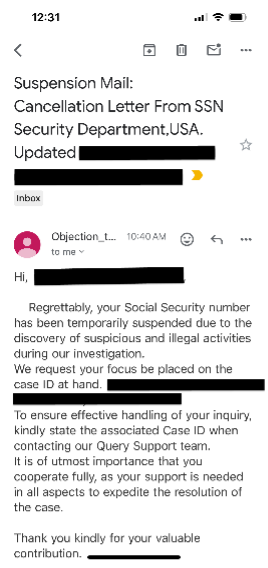
You receive an email ‘from’ Social Security, informing that your account has been suspended. This is the first time you have received an email from the agency that you have problems with your account. You panicked and replied to the email… this is phishing and is a common type of social engineering tactics used by cyber attackers.
Social engineering is a relatively new term that describes malicious psychological tactics used by attackers to manipulate, influence or trick victims into divulging sensitive information or perform ill-advised actions to release personal and financial information, or hand over control over a computer system.
These attacks are especially dangerous as they exploit human error, fear and greed rather than a vulnerability in software. Bad actors primarily do this by pretending to be a known person or legitimate entity. Once inside, the malicious actor can use the stolen credentials to masquerade as the legitimate user to learn about the network defenses, conduct identity theft and steal data.
These attacks can be done in person, over the phone, through texting, email, social media etc. In its 2023 data breach investigation report, Verizon found that 74% of attacks involved the human element and social engineering was at the top of the list. Don’t open the door to scammers!
Here are recent attempts on our network and what to look out for:
In September last year, MGM Resorts in Las Vegas was hit by a ransomware attack. The hackers breached MGM’s network using social engineering, resulting in stolen sensitive data and a massive IT system outage. MGM said the attack also led to a $100 million loss.
Brute force Attacks – why you need a strong password
Brute Force Password Attack is a method of hacking that uses trial and error to crack passwords, login credentials and encryption keys. Attackers, with help of sophisticated cracking machines, will submit many passwords and phrases with the goal of guessing the right one. They use lists of passwords that meet password complexity requirements but are still frequently used passwords based on common words, phrases, numbers, symbols, and characters.
The takeaway: Always create passwords that are uncommon and not easy to guess, or, set up two-step authentication with all of your online accounts.
Learn how passwords are our first line of defense
Learn more about phishing
The IT Security team has put together a 30-minute training to educate departments on phishing and how to protect yourself, your data and our organization’s information. If you would like to have them provide the training, please email us your request at IT_Security_Privacy_Program@urmc.rochester.edu